How to Use Meta AI on WhatsApp (Generate AI Images)
If you use WhatsApp for communication, you can now utilize Meta AI, the company’s … Read more
If you use WhatsApp for communication, you can now utilize Meta AI, the company’s … Read more
You might use several websites and apps every day, but the one that you … Read more

Currently, hundreds of web browser apps are available for Android, but Google Chrome and … Read more
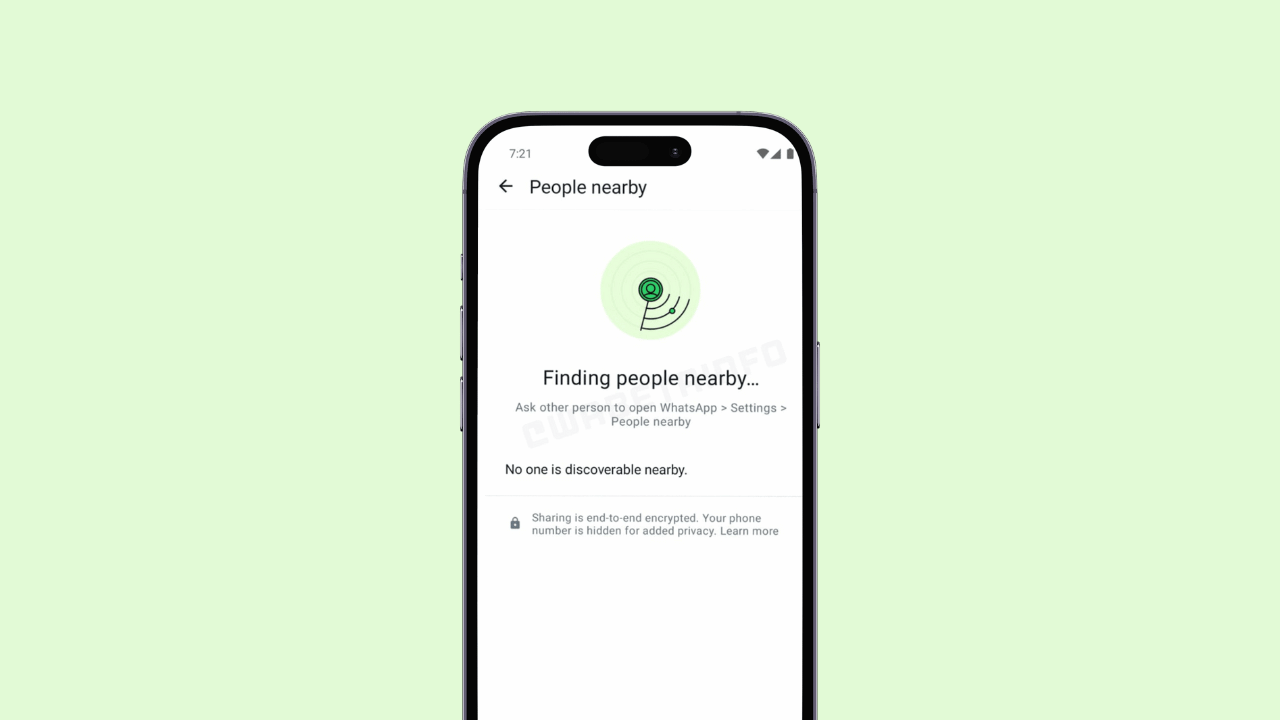
WhatsApp, the popular Meta-owned instant messaging platform, is reportedly testing a new feature that will allow … Read more

Android and iOS have lots of free-to-play tactical RPG/Tower defense games. Such games are … Read more
Let’s admit it: users have always looked for ways to run the PC apps … Read more

If you ask any photographer about the image editing tool, they will probably tell … Read more
Hundreds of video editing apps have been made for Android, offering easy video editing … Read more

As promised earlier, Microsoft released the first preview of the Microsoft Office LTSC 2024 … Read more

Who doesn’t like listening to music? Of course, everyone does. But for a proper … Read more
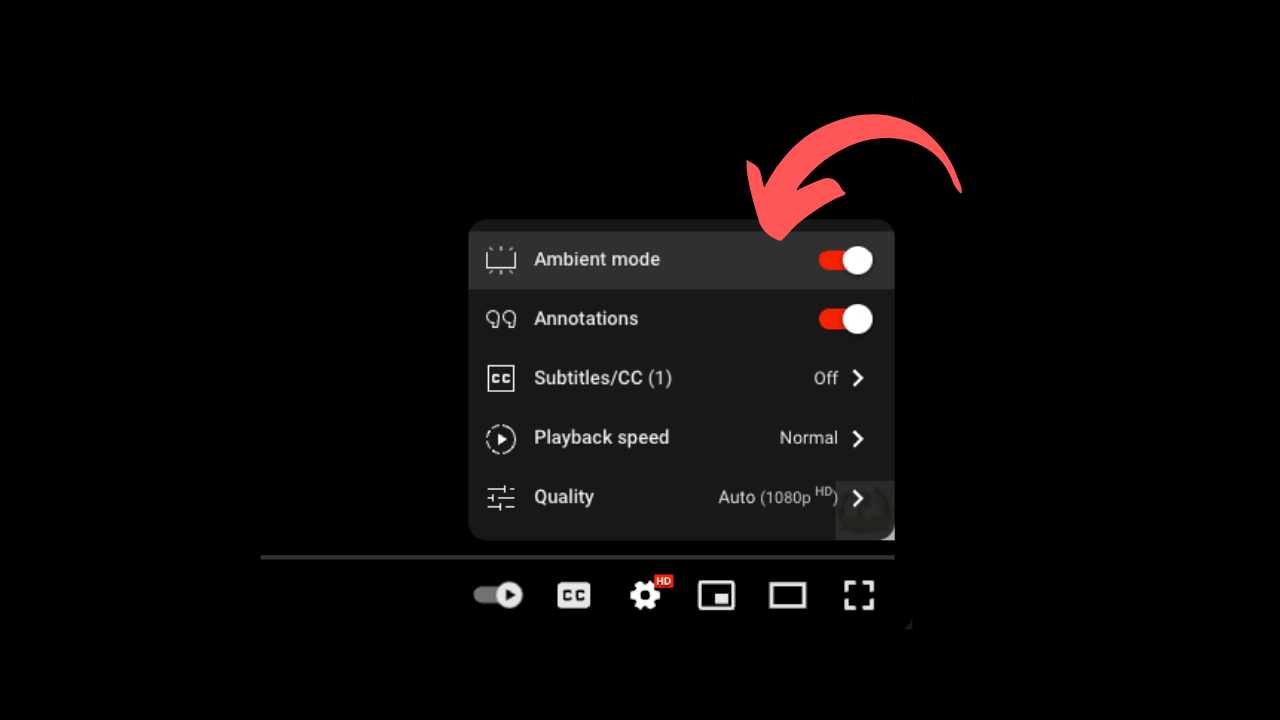
YouTube, the popular video-sharing platform, is reportedly testing a new experimental AI-powered “Ask” button … Read more